What is Certificate Authority (CA)? – Tips to Get SSL Certificate from Certificate Authority
A Certificate Authority is a trusted third party entity that issues digital certificates and manages the public keys and credentials for data encryption for the end user. The responsibility of the CA in this process is to ensure that the company or user receives a unique certificate for an efficient identity authentication.
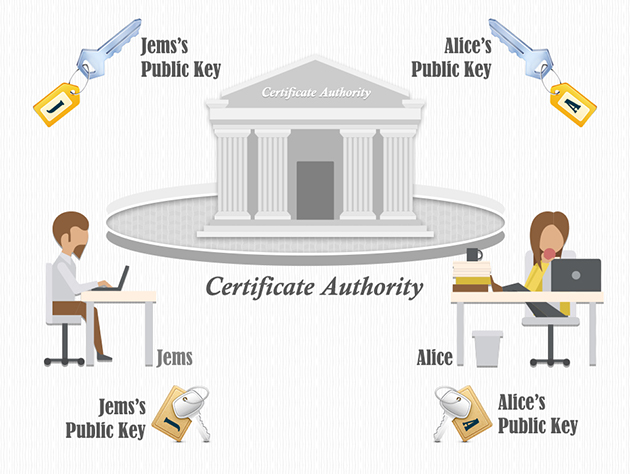
Normally, the CAs have partnerships with financial organizations like the credit reporting agencies to help them with the process of business and identity authentication of the applicants. CAs are a critical component in the field of data security and e-commerce as they guarantee identities of both the parties to each other.
Server administrators and website owners are the customers of a CA. These customers require certificates, which their servers can be configured to use for secure communication with their visitors. These customers expect the certificates issued by their CAs to be included with most of their web servers to establish a smooth and secure connection with the certified servers. The number of web and mobile browsers and applications trusting a particular CA is said to be its ‘compatibility’ or ‘ubiquity’. The ‘CA/Browser Forum’ is self-regulated industry body that has developed extensive guidelines for CA trust.
The Trusted Certificate Authorities:
Here is the list of some of the largest certificate authorities in the market:
- Comodo with 42.6%
- DigiCert (which bought VeriSign’s SSL operations and owns Thawte, GeoTrust, and Rapid SSL) with 15.3% market share
- GoDaddy with 7.7%
- GlobalSign with 4.9%
- Digicert with 2.3%
- StartCom with 0.9%
- Entrust with 0.4%
- Certum with 0.5%
Value means – Total Live Websites using that SSL (as per builtwith.com).
Do I Need a Certificate Authority for My Domain?
No, you don’t need any certificate authority specifically for your domain because these certificate authorities are physical organizations and not something which you can put for installation. However, certificate authorities such as RapidSSL, Sectigo, Comodo are required and responsible for providing SSL/TLS Certificate, which is further installed on websites (domains).
And, the different types and validation levels of SSL/TLS Certificate which you see are provided by these certificate authorities. As a user, what you have to take care of is to purchase the right SSL/TLS Certificate based on your requirements and budget.
Lastly, this question is wrong. And, the question should’ve been, do you have to purchase an SSL/TLS Certificate from an SSL certificate brand. In that case, yes, it’s a compulsion to purchase an SSL certificate from these types of respected Certificate Authorities. If you try installing a self-signed SSL Certificate, then you and your website visitors will face an error message along with a failure to load on the web browsers like Google Chrome and Mozilla Firefox.
How to get SSL Certificate from Trusted Certificate Authority?
Now after applying for SSL certificate, the very next step is to generate the Certificate Signing Request (CSR). Upon finishing the CSR Generation process, CA will provide the customer a private key in a cryptographic form. The next thing to do is to store both the CSR and private key at a safe location on the server or on a local drive.
Now that the CA has received the request for a certificate, they will require that it be validated. All SSL certificates require validation of some sort, which requires action from the end-user. The end-user may be requested to provide documents to prove their identity and business registration depending upon the type of certificate he/she has requested for.
In the case of domain validation (DV), the CA only needs to verify the domain ownership. Once the customer demonstrates it, the certificate is issued immediately. Whereas in the case of OV and EV certificates, the verification process may take up to 10 days as the authority need to verify all the business-related documents. If the documents provided by the customer meet the requirement of CA, the certificate will be issued.