Millions of Websites Affected By WP File Manager Plugin Vulnerability
Update WordPress File Manager Plugin With the Latest Version – Its Vulnerability Can Affect 700K Sites
Recently a few months earlier, in September 2020, the WordPress File Manager plugin has patched and actively exploits a vulnerability that permits full website hijacking.
According to the report of Sucuri, the WordPress security team, the vulnerability has emerged in version 6.4 of the software, which is used for managing file transfers, deletion, copying, and uploads as an alternative instead of FTP.
Here Are the Technical Details of Vulnerability
File Manager Version 6.4 was released on May 5, in that one file was renamed in the plugin during the development and testing phase. Instead of keeping it for only local change, that renamed file was accidentally added to the live project, and the same got published in the newer version 6.4.
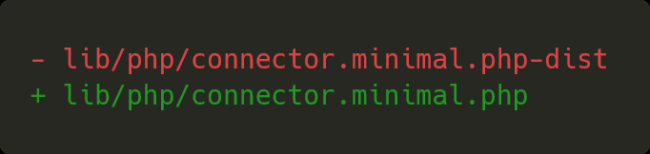
However, that file got noticed and pulled by third-party dependency elFinder, an open-source file manager, and it was used as a code reference. An extension was added to the file with a little tweak of renaming the connector-minimal.php-dist to connector-minimal.php, which was more than enough to trigger a severe vulnerability in this popular File Manager WordPress plugin.
Further, this change allowed unauthenticated users to directly access the file and execute arbitrary commands like uploading or deleting the file, ultimately leaving the website vulnerable to an attack that can completely take it over.
What’s an elFinder?
An open-source package, elFinder, is a file manager for the web, and according to its packagist page, it has been installed more than 2M times, making it one of the popular packages.
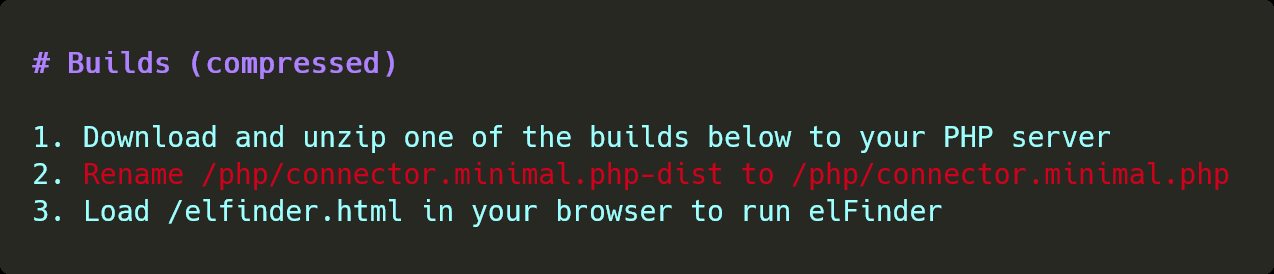
Further, being a file manager, anyone can access its features that provide privileges on the site that can modify, upload, or delete files. But, it’s also aimed for easy setup and use. Though, for that, you’ll require to rename one file according to their installation instructions that you can get from GitHub.
And, a similar thing happened in the case of File Manager. The renamed file left as it’s on the release of version 6.4 that caused this massive vulnerability. While further analysis of this vulnerability also showed that it was possible for bypassing the built-in file upload protection.
The Core Issue Was Due to the Renaming of the Extension on the elFinder
The core issue for this vulnerability was the file renaming on the library named connector.minimal.php.dist file to .php that can be executed directly, even though the File Manager itself didn’t use the connector file. Usually, these libraries include example files that aren’t intended for the “as it is” used without adding any access controls. This file didn’t have any access restrictions that means it was accessible to everyone.
And further, this file could be used for initiating the elFinder command, which was hooked to the elFinderConnector.class.php file.
149 // run elFinder
150 $connector = new elFinderConnector(new elFinder($opts));
151 $connector->run();
Exploit Because of Vulnerability Found in WordPress File Manager Plugin Version 6.4
Its exploit has gained huge popularity once it’s discovered, and it’s even responsible for impacting at a high level with low requirements. It has seen hundreds to thousands of requests through malicious actors that attempted to exploit it. The first attack due to this vulnerability was found on August 31, 2020, the day before the plugin got updated. And, within an hour, it started reporting 1.5K attacks every hour. Further, on September 1, 2020, it got attacked on an average of 2.5K attacks per hour, and on September 2, 2020, it peaked at 10K+ attacks per hour.
Here’s the Brief Timeline of Vulnerability
- May 5, 2020: File manager released version 6.4 that came out with severe vulnerability.
- August 25, 2020: An exploit released on GitHub for the File Manager.
- August 31, 2020: Attacks started appearing against this File Manager WordPress plugin.
- September 1, 2020: The plugin version 6.9 released that fixed this vulnerability.
Summary
Further, the main barrier between development and the deployed solutions is a thin line between security vulnerabilities. Though these mistakes and misfortunes happen, website owners’ responsibility is to keep their site safe. For instance, for this WordPress, File Manager plugin related vulnerability patch is already released. So, if you haven’t patched yet, then you should do it or remove the plugin.
Furthermore, users are suggested to go for known and respected WAF (Web Application Firewall) such as Sectigo Web Firewall. It blocks all the malicious payloads by default through their exploitation rules, policies, and comprehensive protection through their huge database of 10M+ threats, cloud-based technology to deploy and protect the site, and easy to generate detailed reports making complex security easy and simple.