What Is HSTS & How It Provides Secure HTTPS Connections?
Enable HSTS to Secure HTTPS Connections
HSTS is an abbreviation of “Hyper Strict Transport Security.” Originally it was known as “STS” to refer “Strict Transport Security.” But, due to HTTP, the H was added. It’s one of the mandatory things to consider because it helps in eliminating many online attacks, for instance, protocol downgrading, cookie hijacking.
Overview of HSTS
According to RFC 6797, HSTS (HTTP Strict Transport Security) is defined as a web security standard. Its main goal is to create the standard that can help to prevent attacks such as MITM (man-in-the-middle) attacks that often happens due to SSL stripping. Here, SSL stripping means, a technique where an attacker is forcing the browser to connect with a website through an HTTP connection, so they can sniff malicious packets and intercept or modify sensitive data or information.
Here’s the Working of HSTS
On the contrary, if you’ve implied HSTS protocol, the web server will redirect using a 301-response code, which will point it towards HTTPS site and not the HTTP site. The browser will automatically connect with an HTTPS connection from www.aboutssl.org – if HSTS security policy protection is applied correctly using an HTTP response header.
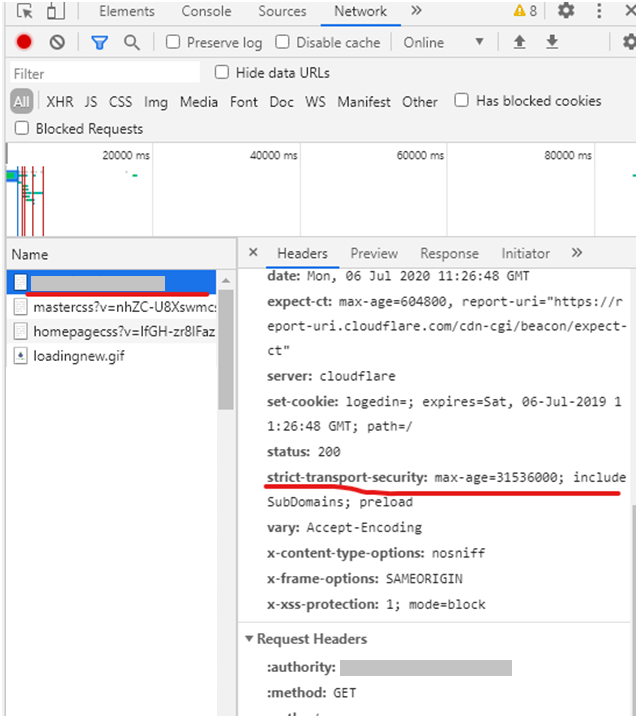
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
Here, the Strict-Transport-Security header provides instruction to the browser that from now every connection with the site and its sub-domains must be in an HTTPS connection for the next year (31536000 seconds) – from the moment this header is received. And the HTTP connection will not be allowed. In case the browser receives any request to load a resource through HTTP, it must first try to convert it into an HTTPS request, and if it can’t, then terminate that connection altogether.
Note:
The Strict-Transport-Security header is sent for a given website that covers a specific domain name. Therefore, if you’ve got HSTS for the domain www.aboutssl.org, it’ll not cover for aboutssl.org, and only www subdomain will be covered. Thus, for getting complete protection, the website must call to the base domain – aboutssl.org and receive a header named Strict-Transport-Security for the domain name along with the directive includeSubDomains.
Benefits of HSTS Protocol
Page Load
Security
For example, the first HTTP request or transfer of data to a website can be intercepted by the cybercriminal who can pretend to be a website by being a middleman between the server and a user. So, if someone sends sensitive information like credit card details, it might first go to the hacker, who then later sends it to the server.
Disadvantage of HSTS
preload – It’s one of the great features of HSTS. But the drawback is that once it’s implemented, it can’t be undone. For instance, after implementing it, for any reason you want to revert it to HTTP, then it won’t be possible, even if you follow all the right steps of phasing out the HSTS protocol. Because browsers won’t delete the old entry from their lists till the new update is provided, and the user downloads it.
includeSubDomains – As the name implies, even if you’ve got unsecured subdomains, it’ll cause an issue. It means, if you’ve subdomains, you’ll have to make those subdomains secure with HTTPS too to keep up with certificates up to date.
max-age – Similar to other attributes as discussed, it’s also one of the mandatory attributes that must be implemented. And, likewise, this one also has a certain downside. For instance, if you ever have to make an unsecured call to the server for any reason, it won’t be possible for the visitors who had cached the policy already.
Here’s How to Implement HSTS on Your Website
HSTS Header on Microsoft IIS Servers
protected void Application_BeginRequest(Object sender, EventArgs e) { switch (Request.Url.Scheme) { case "https": Response.AddHeader("Strict-Transport-Security", "max-age=31536000; includeSubDomains; preload"); break; case "http": var path = "https://" + Request.Url.Host + Request.Url.PathAndQuery; Response.Status = "301 Moved Permanently"; Response.AddHeader("Location", path); break; } }Implementing HSTS on Nginx Server
add_header Strict-Transport-Security 'max-age=300; includeSubDomains; preload; always;'
HSTS Header for Implementing in Apache Server
# Use HTTP Strict Transport Security to force client to use secure connections only
Header always set Strict-Transport-Security "max-age=300; includeSubDomains; preload"
Code to Implement HSTS in lighttpd
server.modules += ( "mod_setenv" ) $HTTP["scheme"] == "https" { setenv.add-response-header = ("Strict-Transport-Security" => "max-age=300; includeSubDomains; preload") }
Steps to Verify HSTS Implementation
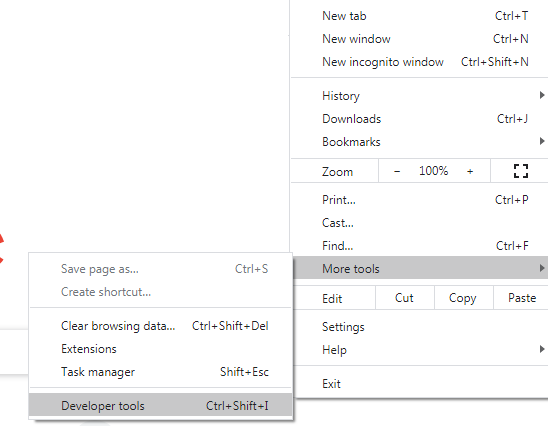
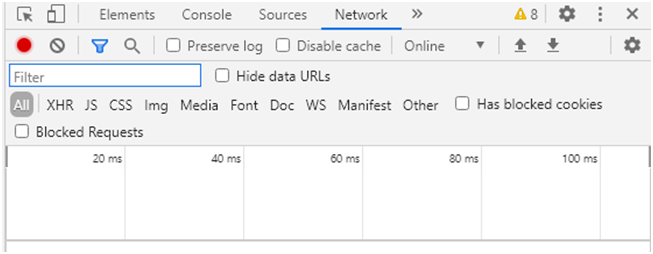
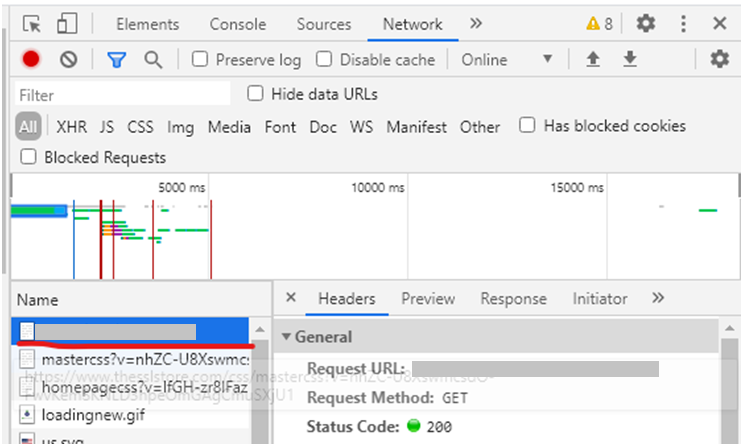
Open the website for which you want to check whether the HSTS has been implemented. For example, open the website you want to verify for HSTS and then click on three dots at the top right side of the browser and select Developer tools from More tools (CTR + Shift + I)