Commonly Seen Security Challenges of Embedded Systems That Shouldn’t Be Ignored
Everyone comes across embedded systems nearly every day in this modern world in one or the other way, and smartphones are one of the most common examples. And no doubt in this digital age, it’s only going to increase. And why shouldn’t its usage increase? It brings so much flexibility and eases to our daily routine.
But, as the technology improves as much, the threats pertaining to it increase too. So, if you’re someone who uses such embedded devices, commonly seen like a smartwatch or else smartphone, you should be aware of some commonly seen security challenges that come with that.

What’s an Embedded System?
Embedded systems are small computer systems that support an electrical system, a special, dedicated function. They are commonly used in most electronics, modern vehicle systems, and nearly all IoT devices.
In other words, an embedded system is a small microprocessor computer hardware system that has software embedded in it for performing any given dedicated function, and it could be a part of a large system or else any independent system. It’s an integrated circuit that’s designed for performing real-time operations of computers.
Nowadays, embedded systems are becoming a staple for both consumers and large industries. Spending on such devices alone is expected to reach $1.2 trillion by 2022 – meaning that manufacturers will need to improve to secure their devices as quickly as possible.
Further, it’s used in various sectors and industries, so security systems should meet different requirements. Security regarding such systems should also be effective – even when a device is not being used or connected to Wi-Fi. Finally, embedded system security needs to be robust and adaptable without compromising on safety.
It can be done by providing an additional layer of protection, along with security protocols such as SSL certification, encryption, and firewalls. However, even with fortified, multi-layer protection, most embedded systems are left vulnerable to attacks. They face numerous security challenges, as it is complicated to create an effective security protocol for all of them.
Some Common Security Challenges That Shouldn’t Be Taken Lightly
Programmers should understand these challenges and identify resolutions specifically designed for these unique, emerging technologies to create viable security solutions for embedded systems.
Let’s examine some major challenges in this area one by one.
1. Many Embedded Systems Are Not Updated or Patched Regularly
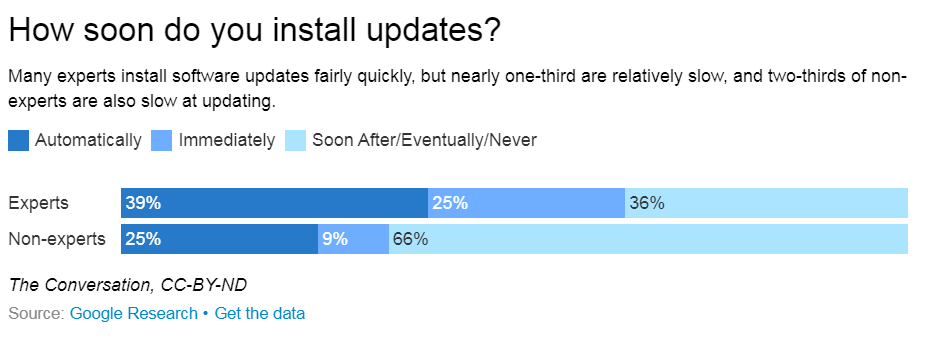
One of the most obvious vulnerabilities is updating and repairing embedded devices to protect the systems from new cyber-attack strategies. Like cellphones or wearables, many of these devices are used for long periods, and embedded systems in vehicles or commercial applications may be used for five, ten, or even more years without being updated. It’s estimated that just 38% of people regularly update security software even when prompted by their devices.
Therefore, security systems should be integrated during the design process and offer customizable and secure code updates to administer patches or rectify software bugs on a regular basis.
2. Attacks Can Be Replicated on Similar Devices
Another unique issue with embedded systems devices is that they are mass-produced with hundreds to thousands of products using the same system. Unfortunately, this creates a perfect opportunity for hackers to attack all identical devices once they figure out how to break into one system.
According to Apriorit, there are three common types of cyber-attacks targeting embedded systems:
- Software-based: Malware, brute-forcing access, memory buffer overflow, web service exploits
- Network-based: MITM (man in the middle), DNS poisoning, DDoS, session hijacking, signal jamming
- Side based: Power analysis, timing attacks, electromagnetic analysis
Therefore, it’s best to incorporate layered security features to create a stronger defense mechanism. It may include encrypted data storage, intrusion detection, and security management systems that identify tampering and alert the user or manufacturer regarding issues.
3. Users Assume That Embedded Devices Aren’t Targets for Hackers
Many end-users are simply unaware of how vulnerable their embedded systems can be, especially if they are not directly used to process or store sensitive data. The fact is that hackers are not just looking for bank accounts and credit card numbers during hacks – they are sometimes seeking email accounts, private data, or simply taking control of the hardware itself.
Since these devices utilize private or sensitive data, they should be effectively secured as they can target viruses and hackers. For instance, an embedded system within a vehicle that controls automatic braking could be compromised, giving an external system the power to stop the vehicle at will. Or an IoT wearable such as a smartwatch that contains financial information through digital payment features could be hacked.
The users of these vehicles or smart fridges or wearables are not aware of the extent of their vulnerability. Even a study shows that 91% of IoT consumers consent to the legal terms and conditions stipulated by the service providers and sellers without reading them.
4. Usage of Embedded Systems Extends Outside the Intended Security Parameter
Most security systems – regardless of the underlying software– are designed and customized for specific hardware or software systems, with firewalls and SSL certifications designed to prevent environment-specific threats. However, if the devices are used for purposes different than originally intended or are altered by the user (think iPhone jailbreak), it could cause issues. Further, if devices are connected to unsecured internet sources (such as public Wi-Fi connection), then embedded systems could be vulnerable to many attacks.
Additionally, many enterprises utilizing embedded systems use legacy devices for as long as possible – in some cases, for decades. While the device lifecycle for some systems may be shorter for consumers (such as a cellphone or IoT wearable), other more expensive technology pieces may not be replaced until they stop working altogether. It creates a true challenge for programmers who should embed security systems and practically predict future threats – or create systems that can be remotely upgraded.
5. Proprietary Embedded Security Protocols Aren’t Recognized by Industry Tools
Unfortunately, the security tools used in most industries and enterprises are not the same as ones utilized in embedded systems. It means that their detection systems and firewalls may not pick up on specific threats targeted at embedded systems – and they also offer little or no security on their own.
Programmers should stress the importance of customized security measures that are layered specifically for the industry and application. It’s the only solution to create a secure embedded system.
Over to You
Embedded systems are an integral piece of technology in the modern world, and their use and functionality are only going to increase. It means the onus lies on the system developers to understand the individual and organizational challenges and provide resilient viable solutions for every use case imaginable.
About the Author :
About Dipti Parmar
 Dipti Parmar is an experienced marketing and technology consultant, helping startups, ecommerce companies, and B2B SaaS brands establish thought leadership in their industry, with innovative strategies and digital transformation initiatives.
Dipti Parmar is an experienced marketing and technology consultant, helping startups, ecommerce companies, and B2B SaaS brands establish thought leadership in their industry, with innovative strategies and digital transformation initiatives.