Private Key – One of the Significant Aspect of the SSL/TLS Certificate
For any websites that process sensitive information, such as personal or credit card information, or usernames and passwords, an SSL Certificate is required to transmit these types of information safely and securely. Moreover, an SSL/TLS Certificate makes any transmitted information unreadable to everyone except the receiving server.
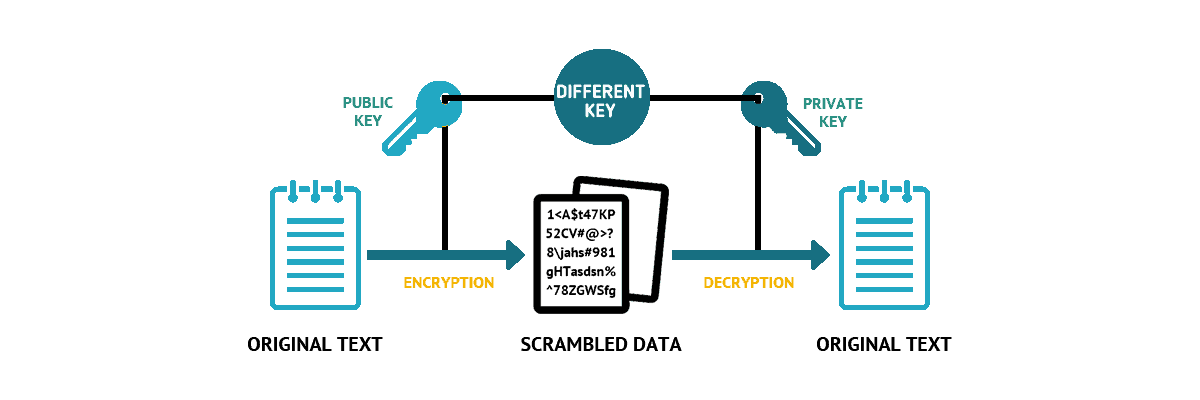
Private Key and Public Key
Each SSL Certificate is issued with two keys that exclusively correspond to that specific certificate. One key is public, which is embedded within the certificate. This key encrypts any information being input into the website to protect the user from someone looking in on the information.
Once the information is submitted to the server, the private key jumps in to decrypt it, allowing it to pass through without being seen between sender and receiver.
The two keys are unique and must be used together to work – missing one key renders the other useless.
Have You Lost Your Private Key?
If you have been issued an SSL Certificate but cannot seem to locate the private key that corresponds with it, there is a way to get that information. If you’re unsure if you’re missing your private key, a quick look at the Certificate’s General Information will let you know. A key that’s active and working will prompt a message stating, ‘You have a private key that corresponds to this certificate.’
For a missing key, this message will not appear, and a blank space will be seen in its’ place. How you go about locating the key will depend mainly on the server operating system being used.
However, there could be more than one reason why a key would be missing. Either the certificate was not installed on the server that generated the Certificate Signing Request (CSR), the request was pending but deleted from IIS, or the certificate was incorrectly installed using the Certificate Import Wizard when it should have been done through IIS.
Comodo Positive SSL
RapidSSL Certificate
Thawte SSL123 Certificate
Retrieving a Lost Private Key
The type of operating system you’re running will dictate how you’re able to retrieve your lost private key. Here’s a quick outline of how to achieve this with each operating system:
Linux OS
On Linux-based operating systems, private keys are usually openssl generated keys. These keys are saved into files using the extension .key or .pem. If you can remember part or all of the name, the key file was saved as you may be able to find it by running the ‘find’ command as follows:
find [search_start_folder] -type f -iname ‘private.key’This [search_start_folder] is used to indicate the directory being used as a starting point for the search. If you’re searching for the file using just a part of the name, you can use an asterisk to help broaden the search. For example, if you know the extension is ‘.key’ and you can’t remember the start of the filename, you can search ‘*.key’ and turn up any file that includes this extension.
Windows OS
If you’re using a Windows OS, you won’t be able to locate your private key in plain text. SSL Certificates that are imported through MMC or IIS automatically have their corresponding private key bound to them. However, if you need to obtain the private key to install the SSL certificate on another server, you would be able to export it using a password protected file.
Here are the steps to do this by first opening MMC Certificates snap-in as follows:
- Win+R > mmc.exe > OK > File > Add/Remove Snap-in > Certificates > Add > Computer account > Next > Local computer > Finish > OK
- After this step, if the certificate request was not completed, go to Certificate Enrollment Requests > Certificates; Or, if the request was already completed, go to Personal > Certificates
- Then, right-click on the certificate entry and click All Tasks > Export to get to the export wizard
- Once this has been exported, you will get a .pfx file with the key contained within it. You can then convert that file to plain text, using a converter to switch it from a .pfx file into a PEM encoded file
Mac OS X
Through the Mac OS X, it’s a fairly simple process to navigate through, first opening the ‘/etc/certificates’ folder. Then, you should be able to locate the key file, which is likely named using a ‘.key’ or ‘.pem’ name.
Tomcat
Usually, the private key on Tomcat is stored in a Java keystore file, which is password-protected. Retrieve your key; it would first need to be converted into .pfx/.p12. Here is the command to use to get this started:
- keytool -importkeystore -srckeystore keystore.jks -destkeystore keystore.p12 -deststoretype PKCS12 -srcalias -srcstorepass -srckeypass -deststorepass -destkeypass
Replace the entry “keystore.jks” with the actual name of the keystore that holds the key you’re looking for. Also, replace “keystore.p12” with the name of the .pfx/.p12 file into which the keystore will be converted.
To secure the integrity of the newly created .pfx/p12 file, you’ll need to refer to the alias, the keystore password and the key password values detailed in the keystore generation.
After this file has been created, it can then be converted into PEM format using OpenSSL or using a conversion tool.
cPanel
You may want to use SSL/TLS Manager by clicking on the SSL/TLS Manager on the cPanel home page. Click on the ‘Private keys’ button to open a new screen, where you’ll see a list of private keys created in that particular cPanel account. By clicking on the ‘View & Edit’ button, you’ll be able to view the private key in encoded and decoded format.
Alternately, opening the file manager from the cPanel home will let you search for the ‘SSL’ folder, then click on the directory of ‘keys.’ You’ll see the private keys within a navigation panel, which you can use to download or open the key in plain text.
There are a variety of other operating systems you may be using, each with its different way of retrieving your SSL Certificate Private Key. If you are unable to locate this key using the tips outlined above, you can always generate a new CSR, and private key to reissue the certificate. If you do have to take this step, ensure that this time your private key is safe, so you don’t have to go through this trouble again.
AboutSSL’s Best Stuff
About Chloe Bennet
 Chloe Bennet is a teacher and educator at UKWritings , academic essay writing service.
Chloe Bennet is a teacher and educator at UKWritings , academic essay writing service.
See Author’s Website


