In other words, unlike say a traditional on-premises environment where the host and user are the same company, a cloud environment involves multiple parties.
Yes, there is the host and a customer, but there are other customers as well — i.e., multi-tenancy — which adds a unique dynamic, and security complication. There’s an expectation, much like in an apartment complex, that hosts and tenants will keep the environment safe. This is in contrast to managing a privately hosted cloud via your own data center.
Second, the burden of security responsibility varies based on the cloud services provided.
For example, in an infrastructure-as-a-service (IaaS) arrangement, the cloud services provider (CSP) is responsible for securing the physical infrastructure and virtualization stack, but the rest — e.g., hosting, data, middleware, application, etc. — falls onto the cloud customer.
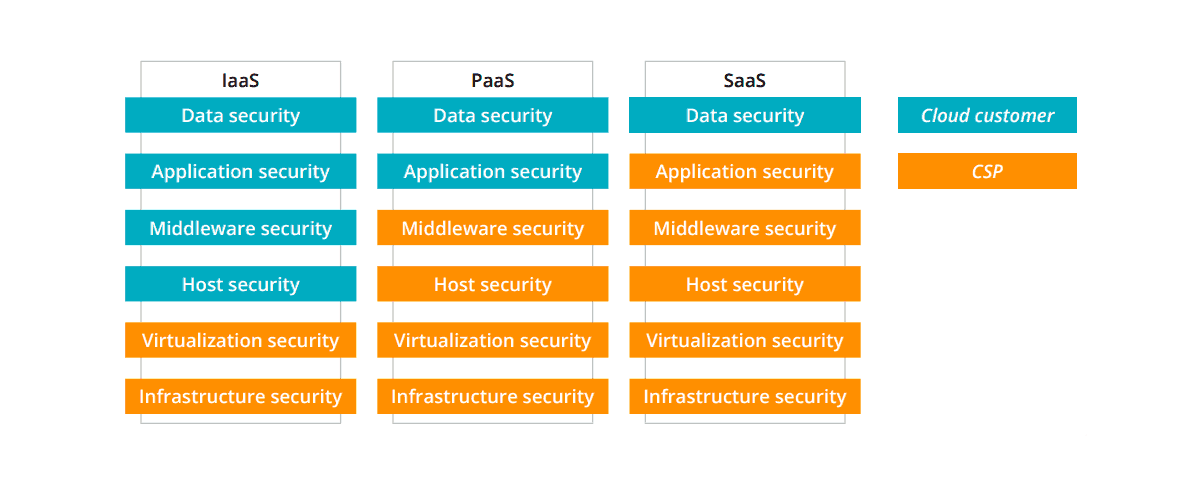
On the other hand, as you can see from the chart above, in platform-as-a-service (PaaS) and software-as-a-service (SaaS) arrangements, the CSP is responsible for everything except the application and data security (and in SaaS, everything but data security).
Yes, this post is about techniques and practices, but it’s not possible to discuss those without setting the context about who’s responsible first. That burden of responsibility will vary across companies, industries, focus-areas, and digital goals.
For example, a bank that’s willing to use cloud services would likely look at IaaS, while a small business with lots of online tools has to look at SaaS security practices.
With that context in place, let’s discuss cloud security best practices.
Infrastructure & Virtualization Security
Infrastructure
In terms of securing cloud infrastructure, you are looking at two key areas: the actual, physical infrastructure which is your data center and second, network security.
Physical Security
To secure your data center, you must ensure that you are restricting access to the facility to only authorized persons. Specific steps include access control measures such as access cards, 24/7 video surveillance monitoring, and an on-site security team, for a start.
You must also have contingencies in place to prevent data loss caused by natural disasters, an on-site incident, loss of power, and other risks. Within these contingencies, a data recovery plan is necessary along with other redundancies.
Network Security
You must combine network monitoring, filtering, and access control to isolate malicious virtual machines, mitigate distributed-denial-of-service (DDoS) attacks, and suspicious access/logins.
In this respect, you must install firewalls, security gateways, and anti-DDoS systems and pair those with a network security team to monitor and promptly respond to incidents.
Virtualization Security
The goal of virtualization security is to keep application programming interfaces (API) secure as well as isolate tenants in your virtual machines (VM) or containers.
You must also ensure that virtual network transmissions are secure. As with network security, recommended solutions include firewalls and anti-DDoS systems. You can also look into anti-virus gateways and intrusion prevention systems (IPS).
Host & Middleware Security
Host Security
The idea here is to protect what you’re hosting on your servers — e.g., client data, application data, APIs, etc. — from malicious code, intrusion, and vulnerabilities.
Standard solutions for this problem include acquiring an anti-virus system to detect and sandbox malicious code, an IPS, and a regular patch update cadence.
However, host security is not limited to just systems; there’s a processing element involving you to:
- Disable idling or unused ports
- Install and enforce access control
- Remove unnecessary processes and old instances
- Monitor logs and incidents
Middleware Security
Containers
When it comes to containers, your primary goal (assuming the infrastructure security is already in place) is to restrict access to the repositories. In addition, you must ensure that the containers are correctly configured, to prevent errors and vulnerabilities.
APIs
To secure APIs, you must have policies, processes, and systems in place for the following:
- Authenticate APIs so as to ensure only legitimate API requests are coming through and, in turn, denying suspicious ones.
- Monitor APIs: You should have a system in place to monitor APIs, especially for key API health metrics such as error-rate and delays.
- API Log Management: The general idea is to monitor who/what and when are invoking APIs, ensuring data is being transmitted securely, and monitor for suspicious activity.
Databases
To secure databases, your starting point should be to conduct database audits. You can use these audits to evaluate the security risks posed to the database, monitor behavior, and set-up an incident monitoring and alert system.
Resource Management Platform
The purpose of a resource management platform is to monitor, detect, and respond to any suspicious and unauthorized activity. You can start implementing this with an internal security information and event management (SIEM) process.
Application System & Data Security
Application Systems
The idea here is to protect what you’re hosting on your servers — e.g., client data, application data, APIs, etc. — from malicious code, intrusion, and vulnerabilities.
Standard solutions for this problem include acquiring an anti-virus system to detect and sandbox malicious code, an IPS, and a regular patch update cadence.
However, host security is not limited to just systems; there’s a processing element involving you to:
- Identity Authentication
- API Access Security
- Account Management
- Role Authentication
Data Security
In terms of data security, your objective is to prevent data from leaking or getting damaged. In addition, you must also ensure network transmissions are secure and that your data is shielded from forgery, theft, tampering, and other malicious activities.
The first step is to encrypt the data in its storage and transmission forms. Likewise, you must also ensure that the data of each tenant is isolated from the other. As noted earlier, you could also implement a database audit to identify potential risks and close them early.
The second step is to ensure that the data is only being transmitted securely. This involves enforcing HTTPS protocols via SSL/TLS. In fact, this is a regulatory requirement in PaaS or SaaS-based offerings involving online payment, such as Stripe and Shopify.
Comodo Positive SSL
RapidSSL Certificate
Thawte SSL123 Certificate
Next, the third step involves processes such as access control and others to ensure that only authorized persons (to the exclusion of all others) have access to the data and that too if it’s required for their job.
Finally, you must have measures in place to recover that data in case of a breach or other disaster (i.e., disaster recovery).
Can Your Business Handle All of That?
You can’t implement a proper cloud security effort without the necessary tools, experts, and processes. However, this requires a significant investment on top of the cost of infrastructure and other fixed overheads. All of this is doable for enterprises such as multi-national banks, but not so for small and medium-sized businesses (SMB). In fact, even some large businesses might balk at the cost of setting up and maintaining their own data centers.
In such cases, you should look at outsourcing cloud management and support services. This could involve relying on a public cloud host for IaaS and PaaS services as well as a managed service provider to ensure your IaaS/PaaS is properly configured and deployed.
AboutSSL’s Best Stuff
Related Articles:
About Jeremy Stevens
 Jeremy Stevens has spent over half a decade working in the tech industry. Besides learning new things about software and IT, one of his passions is writing & teaching about technology. He is working with Power Consulting and helps produce and edit content related to IT, covering topics such as hardware & software solutions for businesses, cloud technology, digital transformation, and much more.
Jeremy Stevens has spent over half a decade working in the tech industry. Besides learning new things about software and IT, one of his passions is writing & teaching about technology. He is working with Power Consulting and helps produce and edit content related to IT, covering topics such as hardware & software solutions for businesses, cloud technology, digital transformation, and much more.


