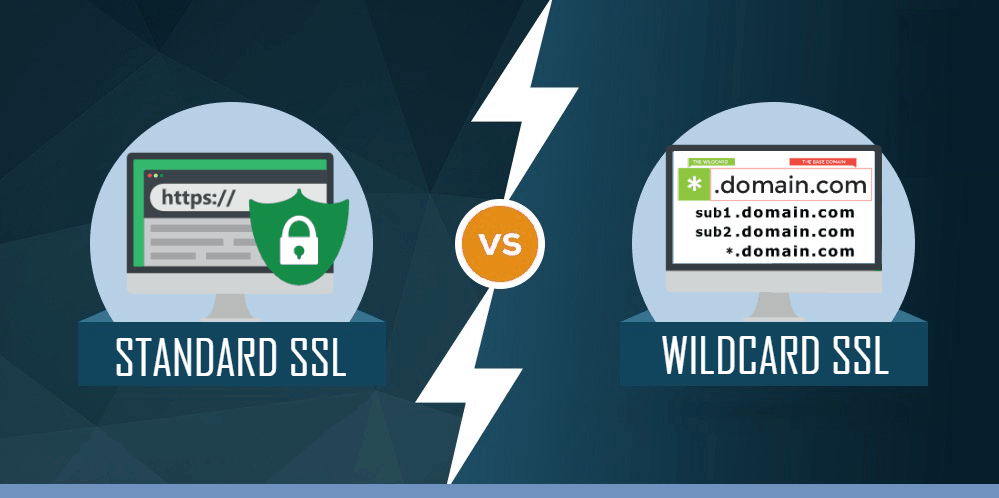
What’s the Difference? – Standard SSL vs Wildcard SSL Certificate
Understanding the difference in functionality between Wildcards and Single Domain SSL certificates
But with this influx of new customers, there are a lot of people who don’t understand SSL, SSL/TLS certificates, and what they need to select to best secure their websites. That’s why we’ve written this guide comparing standard, single-domain SSL certificates with Wildcards.
Let’s start with a quick refresher on how ssl certificate works before we get into the specifics.
See Also: Wildcard SSL vs SAN SSL Certificate
A short rundown of SSL/TLS
When you purchase and install an SSL certificate, you can migrate your website to HTTPS and start making secure connections. The way this works is a little complicated, but we’ll try to keep it simple.
Every operating system has a trust store, a collection of CA root certificates, and their public keys that are saved on your machine. From those root certificates, the CA issue, something called an Intermediate root. Because root certificates are so valuable, issuing directly from them is too risky as any misissuance that requires revocation of the root would invalidate every descendant certificate it’s chained to. Obviously, that’s not a risk worth taking.
So sign the intermediates with their roots’ private keys and issue off the intermediate. When we say issue what we really mean is a sign. You will create a Certificate Signing Request on your server (along with the private key) and then send the CSR to the CA. They use the CSR to populate the details in your certificate (after they validate the information provided) and then sign it with one of their intermediate roots’ private keys.
When someone visits your website, their computer will download the SSL certificate and then try to trace the signature back to the certificate whose private key was used to sign it. Once it reaches that certificate, it checks who signed it and continues following the chain until it reaches one of the CA roots in their trust store. If the signatures do chain back to a root, the browser will extend trust to the website. If not it creates an interstitial error.
Lets Talk About How SSL Certificates Facilitate Encryption
There are two kinds of encryption at work when it comes to SSL. The first type is called asymmetric encryption. There is a publicly available key for encryption, but only the server has possession of the private key that can decrypt. Asymmetric encryption is one-way encryption. That’s great for secure key exchange but untenable for regular communication. So once the encrypted connection between the client and server begins, they switch to symmetric encryption. With symmetric encryption, a pair of matching keys can be used to both encrypt and decrypt, making it a far better choice for communication.
The other advantage that symmetric encryption has over asymmetric is performance. This is owing to the key size. A private key is typically 2,048-bit, much more robust than its symmetric counterparts, which means it would be harder to crack but also added latency to a connection. In fact, that’s been one of the biggest challenges facing the cryptographers that work on new versions of SSL/TLS shortening the time that the handshake takes. With the release of TLS 1.3 its been cut down to a single roundtrip, but there was a time where the handshake made the entire website slower. Again, that’s no longer an issue but it does illustrate why using a 2,048-bit key for communication is not advisable.
Symmetric keys are typically 256-bit length, which has less hardness (the measure of strength for encryption) but offers much better performance.
And just because the key size is smaller doesn’t make symmetric encryption less secure. It would still take a supercomputer over 1,000 years to crack a 256-bit symmetric session key. For what it’s worth it would take 4-quadrillion years (that’s a real number) for the same computer to crack a 2,408-bit key.
At any rate, the communication that takes place between the server and the client is encrypted symmetrically.
Now Let’s Talk About Single Domain SSL Certificates
Standard SSL certificates are available at three different validation levels.
Domain Validation simply requires server authentication. Organization Validation involves light business vetting and places verified organizational information in the certificate details. Extended Validation requires a deep business vetting but also places the verified organizational name prominently in the address bar.
Top Most Standard SSL Certificates & It’s Providers
What is a Wildcard SSL certificate?
- Mail.website.com
- Members.website.com
- Development.website.com
- Loging.website.com
As you can see, a first level sub-domain comes right before the domain name. Lots of websites use sub-domains and while you can use standard SSL certificates to encrypt each one individually, that would have cost-prohibitive.
Wildcards allow websites to encrypt all of their sub-domains with a single certificate. This saves time and money. And best of all, if you add a sub-domain you don’t even have to re-issue the certificate, just reconfigure your server and your Wildcard will secure the new sub-domain, too.
There are a couple of drawbacks to Wildcards though.
First and foremost, from a security standpoint, you’re potentially inviting greater risk because the same private key will be associated with all of your sub-domains. So, if your private key ever gets compromised you won’t be able to limit the damage, all of your sub-domains will be compromised, too.
Additionally, Wildcards are not available at the Extended Validation level. This is also for security reasons.
Top Most Wildcard SSL Certificates & It’s Providers
| Brand | SSL Product | SSL Type | Issuance Time | More Details |
| Positive SSL Wildcard | DV SSL | Immediate | Read More | |
| Premium SSL Wildcard | OV SSL | 1-3 Days | Read More | |
| RapidSSL Wildcard | DV SSL | Immediate | Read More | |
| SSL123 Wildcard | DV SSL | Immediate | Read More | |
| True BusinessID Wildcard | OV SSL | 1-3 Days | Read More | |
| Secure Site Wildcard | OV SSL | 1-3 Days | Read More |
What is best for your website?
| Main Features | Comodo Positive SSL | Comodo Positive SSL Wildcard |
|---|---|---|
| Certificate Authority | ||
| 1 | 1 + all one level sub-domains | |
| $7.27/yr | $72.31/yr | |
| www.domain.com, domain.com |
domain.com, www.domain.com, login.domain.com, mail.domain.com |
|
| Personal Websites/Blogs | Personal Websites/Blogs | |
 |
 |
|
| Domain | Domain | |
 |
 |
|
| Within Minutes | Within Minutes | |
| up to 256-bit | up to 256-bit | |
| 2048 bits | 2048 bits | |
| Medium | Medium | |
| Domain name displayed on certificate details | Domain name displayed on certificate details | |
| Unlimited | Unlimited | |
 |
 |
|
| $10,000 | $10,000 | |
| 30 days | 30 days | |
 |
 |
|
 |
 |
|
 |
 |
|
| 99% | 99% | |
 |
 |
|
 |
 |
|

